When you visit an encrypted website, the connection between the source of the web page and your browser is secure. Encryption ensures users’ browsing habits are safe from hackers’ prying eyes, but phishing scammers have found a way to adopt it for their own schemes.
Phishers use encrypted sites to scam
A keylogger found in HP laptops
Key points from Protenus’ new report!
Watch out! More ransomware attacks incoming
What you need to know about malware
Why Nyetya is more threatening than WannaCry
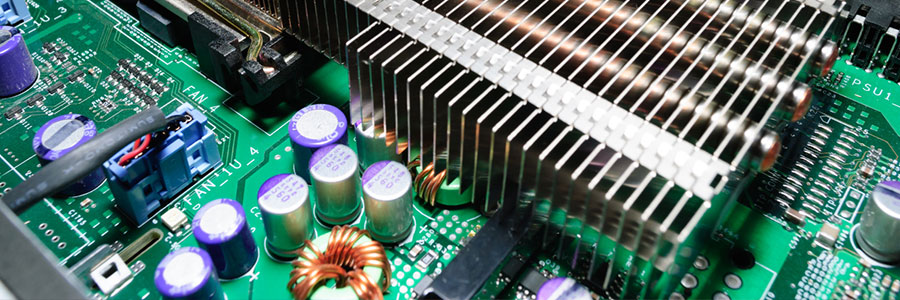
Firmware: the threat most users overlook
Are your printers safe?
3 Reminders for HIPAA compliance in 2017

Although totally necessary, data privacy regulations are often a gigantic headache. And king among the various compliance standards is HIPAA. Despite the legislation’s enactment back in 2003, the rules governing electronic medical records and protected health information continue to change and evolve every year.
Ransomware demands more victims for freedom

Ransomware has become a fast-track for making money for some hackers this holiday season. But instead of just demanding a small payment for the decryption code that will unlock their computers, some hackers are demanding that victims sacrifice two other friends to ensure they receive the code they need.
- 1
- 2