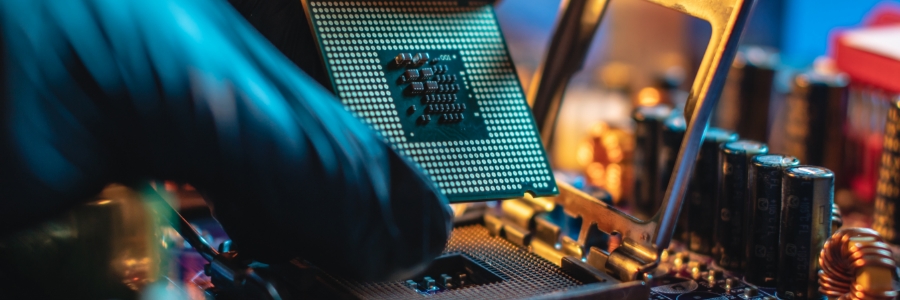
When it comes to replacing your company’s servers, you should review aspects of your existing server infrastructure and consider the implications of the upgrade. Answering questions related to reliability, performance, security, and scalability will allow you to make the right decisions and ensure the upgrade aligns with your company’s long-term goals.
Is it time to upgrade? Key considerations before replacing your servers
How to increase the life span of your business computer and hardware

With time, pesky dust and dirt build up sneakily within your device and can lead to overheating or failure. Heed our expert advice and make your computer's care a breeze.
Regularly clean computer components
Make it a habit to keep your monitors and peripherals clean by gently wiping them with a microfiber cloth specifically designed for computer components.
Keep your work devices clean and running smoothly with these tips

It's no secret that a clean work environment is more productive than a cluttered one. The same principle applies to your computer and mobile devices. If you allow them to accumulate dirt and dust, you're going to start seeing glitches and hardware failures — both of which will affect your productivity.
Advantages of dual monitor systems
If you're like most business owners, you're always looking for ways to improve your employees' productivity. One way to do this is by upgrading your office computers with dual monitor systems. Here are the benefits of using two monitors per desktop and how this setup can help your business achieve its goals.
A guide to choosing the perfect mouse for you
What is firmware and why is it important?
Technology evolves quickly. The features of a phone that came out two years ago are likely very different from the features of the most recent model. It's the same with printers, laptops, and other devices in your office — newer models with better features are introduced to the market yearly, so you need to keep up with technology trends to stay competitive and even compliant with security regulations.
Easy tips to increase your computer’s longevity
7 Tips to reduce PC power consumption
A guide to choosing the right business projector
4 Ways to keep your servers cool

For any organization, servers are important for storing business data. This is why you should make sure that your servers are well-maintained. If not, their operating temperatures will rise, which can lead to server instability or even data loss. Read on to learn how to keep your servers at ideal temperatures.